How to Secure Your Online Accounts: A Step-by-Step Guide to Cybersecurity for Beginners
Learn how to protect your emails, social media & bank accounts from hackers with this simple, step-by-step cybersecurity checklist. Stay safe online!

How to Secure Your Online Accounts: A Step-by-Step Guide to Cybersecurity for Beginners (2025)
In today’s digital world, your online accounts are your identity.
From your email and social media to banking and shopping profiles—each one holds valuable personal data. And unfortunately, cybercrime is rising: over 2,200 cyberattacks occur every day, and 95% of them start with a stolen password.
But here’s the good news: you don’t need to be a tech expert to stay safe. With a few smart habits, you can drastically reduce your risk of being hacked.
In this guide, we’ll walk you through seven proven steps to secure your online accounts—even if you’ve never thought about cybersecurity before. By the end, you’ll have a personalized security checklist you can implement in under an hour.
Step 1: Use Strong, Unique Passwords and Never Reuse Them
Weak or reused passwords are the number one cause of account breaches.
What makes a strong password?
- At least 12 characters long
- Mix of uppercase letters, lowercase letters, numbers, and symbols
- No personal information such as birthdays, names, or common words
- Not based on dictionary words, even with character substitutions like “P@ssw0rd”
Bad example: Michael123
Good example: 7m$Q!vL9#pKx
Memorizing dozens of complex passwords is impractical. That’s where a password manager becomes essential.
Pro Tip: Use a trusted password manager like Bitwarden (free) or 1Password (paid). It generates, stores, and auto-fills strong, unique passwords for every site—so you only need to remember one master password.
We’ll cover password managers in more detail in an upcoming guide—subscribe to be notified when it’s published.
Step 2: Enable Two-Factor Authentication on All Important Accounts
Even a strong password can be compromised. Two-factor authentication (2FA) adds a critical second layer of protection by requiring a second form of verification—typically a code from your phone or an authentication app.
Enable 2FA on these accounts:
- Email (Gmail, Outlook, etc.)
- Social media (Facebook, Instagram, X)
- Banking and financial services
- Cloud storage (Google Drive, Dropbox, iCloud)
Best 2FA methods, ranked by security:
- Authentication apps such as Google Authenticator, Authy, or Microsoft Authenticator
- Physical security keys like YubiKey
- SMS text messages — only use this if no other option is available, as SIM-swapping attacks are increasingly common
Action Step: Visit twofactorauth.org to check which of your accounts support two-factor authentication—and enable it immediately.
Step 3: Run a Security Checkup on Your Major Accounts
Google, Apple, Microsoft, and other major platforms offer free, automated security reviews that can identify vulnerabilities in seconds.
- Google: myaccount.google.com/security-checkup
- Apple: Go to Settings > [your name] > Sign-In & Security
- Microsoft: account.microsoft.com/security
These tools will:
- Alert you to suspicious login attempts
- Show third-party apps with access to your data
- Recommend security improvements based on your usage
Set aside 10 minutes today to complete these checkups—you may discover risks you weren’t aware of.
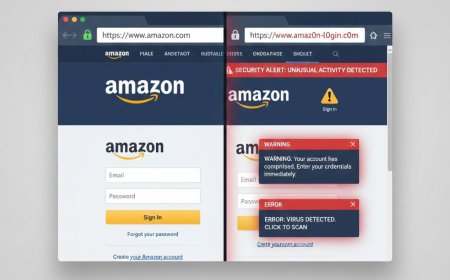
Step 4: Learn to Recognize and Avoid Phishing Attacks
Phishing involves deceptive emails, texts, or websites designed to trick you into revealing passwords or financial information.
Common signs of a phishing attempt:
- Urgent or threatening language (“Your account will be closed in 24 hours!”)
- Slightly misspelled URLs (e.g., “amaz0n-login.com” instead of “amazon.com”)
- Requests for passwords, credit card numbers, or personal identification
- Unexpected attachments or links from unknown senders
Always:
- Hover over links to preview the actual destination URL
- Log in directly through the official website or app—never click links in unsolicited emails
- Use browser extensions like uBlock Origin or Netcraft to block known scam sites
Test your phishing awareness with Google’s free Phishing Quiz.
Step 5: Keep All Software Updated
Outdated software often contains known security flaws that hackers actively exploit.
Ensure automatic updates are enabled for:
- Your mobile operating system (iOS or Android)
- Your computer’s operating system (Windows or macOS)
- Web browsers (Chrome, Firefox, Safari, Edge)
- Antivirus and security software
The 2017 WannaCry ransomware attack infected over 200,000 computers worldwide—all running outdated versions of Windows that had not installed available security patches.
Step 6: Use Privacy-Focused Browsers and Search Engines
Standard browsers often track your activity across the web. Switching to privacy-respecting alternatives reduces data collection and lowers exposure to malicious ads.
| Tool | Why It’s Better |
|---|---|
| Brave Browser | Blocks ads and trackers by default without requiring extensions |
| DuckDuckGo | Does not store your search history or build a profile of your interests |
| Firefox with privacy extensions | Highly customizable and open-source, with strong security settings |
Avoid accessing sensitive accounts (such as banking or email) on public Wi-Fi unless you are using a reputable virtual private network (VPN). We’ll cover trustworthy VPN options in a future article.
Step 7: Set Up Account Recovery Options
Even with strong security, you may get locked out. Prepare for emergencies by configuring recovery methods in advance.
- Add a reliable recovery email address and phone number to all critical accounts
- Save two-factor authentication backup codes in a secure location—such as your password manager or a printed copy stored safely at home
- Use account recovery features like Google’s “Trusted Contacts” or Apple’s “Legacy Contact” to grant emergency access to a family member
Your 2025 Cybersecurity Checklist
Save or print this list and complete each item:
- [ ] Use a password manager for all accounts
- [ ] Enable two-factor authentication on email, banking, and social media
- [ ] Run security checkups on Google, Apple, and Microsoft accounts
- [ ] Revoke access for unused third-party apps
- [ ] Learn to identify phishing attempts
- [ ] Turn on automatic software updates
- [ ] Switch to a privacy-focused browser
- [ ] Store 2FA backup codes securely
What to Read Next
Now that your accounts are better protected, explore these related guides:
- Best Free Password Managers Compared (2025)
- How to Spot a Fake Website in Seconds
- Is Public Wi-Fi Safe? How to Browse Securely Anywhere
Final Thoughts
Cybersecurity isn’t about fear—it’s about taking practical, manageable steps to protect your digital life. By completing the actions in this guide, you’ve already surpassed the security practices of most internet users.
Stay informed, stay cautious, and never stop improving your online safety habits.
Found this guide helpful? Share it with a friend or family member who could benefit from stronger online security.
Want more practical tech advice? Subscribe to our newsletter for weekly tips on staying safe and productive online.
What's Your Reaction?
 Like
1
Like
1
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0